How To Check Firewall Settings On Mobile
Protect your computer devices from malicious traffic, viruses, and cyber attackers by understanding how to check your proxy and firewall Settings, therefore enabling whatever of them to avoid IP vulnerability.

Although proxy and firewall work completely differently, many withal confuse the pregnant and usage of these network securities. Deciding on a choice sometimes is often a challenging factor for some. That's understandable every bit not everyone gets it right in terms of their technicalities, not to talk of the setup.
While Firewall utilization serves as an unwanted traffic block, proxies are like a network link. Both have their peculiar features, settings, and functionalities which foster a secured connection workload and prevent network vulnerability.
At that place are several types of these network security, but one amazing matter is, proxy as a server has its types, and Firewall as well do of which application proxy gateway is one of them. Though the aforementioned is a firewall blazon, information technology acts as a reverse proxy; quite expensive, it works at an application layer and is most advanced over others that piece of work at the network or transport layer.
When data is coming from exterior, this type can restructure legitimate data trying to pass through that is non well structured, then its interface can accommodate information technology; it can change IPs to avoid web detection and shop previously searched data in a enshroud.
However, in this article, we are non just to get y'all briefed but rather to enlighten you about how to cheque the settings of these ii networking securities in your devices and enable their commands to finer secure and authorize a user-friendly network interface.
Proxy

A proxy is a server that works as an intermediary between the users and the network they desire to access. Proxies make requests on behalf of the clients and stood-still like a middleman. For case, instead of straight access to the Internet to retrieve your web page of interest which volition expose your real IP accost visibility, using a proxy, all y'all need to do is transport the asking of the web address to the proxy, and the proxy will mask your IP address and assign it'south own IP accost to access the Internet and recollect the information.
This is so good considering your real IP address is hidden by the proxy, therefore safeguarding any vulnerable situations. 1 favorable thing most using a proxy is that information technology has a cache, which automatically saves all web page accessed in its database and then that whenever a such a request is needed, it just retrieve it and send information technology to your computer IP instead of starting a fresh search over once more.
Pros of Proxy :
- One major pro of a proxy is that, since it stands as an intermediary between clients and their website of interest while trying to access the net upon sending a asking to your proxy server, instead of using your real IP address to make a spider web request and retrieval, information technology sends its own IP address instead, therefore masking your real IP accost from revealing publicly.
- Knowing a proxy helps shade your real IP accost somewhat makes you appear anonymous, and with that, access tin can be gained to geo-restricted content and location without whatever fearfulness of website detection that can issue in any class of ban.
- With the rotating feature of some proxy servers, web scraping can be initiated. Web scraping enables you to get numerous data from different websites, which in the normal stage would block users, but with a proxy, IP addresses tin can be changed oft to avoid any blockage.
- With a proxy, online data can be retrieved apace, and what exercise I mean? A proxy has a cache that stores previously visited web pages, and then when a request of the same is sent, instead of sending information technology to the Internet to outset a fresh search, information technology checks its enshroud database and retrieves requested web data; hence no bandwidth is used.
- Proxy servers can exist configured to block access to sites and spider web pages known to contain malicious malware lawmaking in the form of phishing links and viruses. It can filter information or requests from external sites, thereby preventing unauthorized admission to pages or sites from getting into hackers' zone.
Cons of Proxy :
- Although a proxy can brand a request on behalf of the client, it does not encrypt data by default. Thus they are not completely secure. The proxy administrators tin besides sniff at your web activities.
- Non all traffic is routed. HTTP proxy works with HTTP traffic, the same as HTTPS works with its traffic, and SOCKS does the same. Non otherwise interwoven.
- Applications tin can bypass proxy, as proxies piece of work from the application layer. In fact, almost applications practise not respect default proxy settings, and as such, yous need a 3rd-party app like Proxifier to strength all applications to use proxies.
How To Check Proxy Setting?
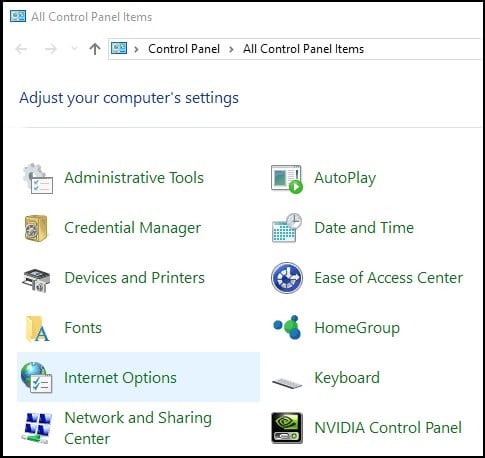
This Footstep goes for all Windows versions, you can observe the proxy settings via the Control Panel on your figurer.
Pace one: Click on Start
Stride 2: Open up the Control Panel.
Step 3: Click on Net Options.
Step four: In the Internet Options, become to Connections > LAN settings.
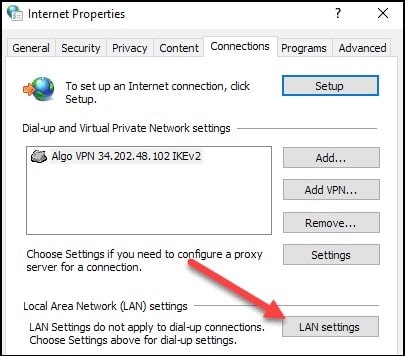
Two configuration options will display, i.due east., Automated configuration or Proxy Server setup.
- If 'Use automatic configuration script' is checked, it means that yous accept configured PAC proxy in your arrangement. Y'all can obtain the path to the PAC file from the "Script Accost" section.
- If "Use a proxy server for your LAN' is checked, you tin obtain Proxy Host and Port from the "Accost" and "Port"sections.
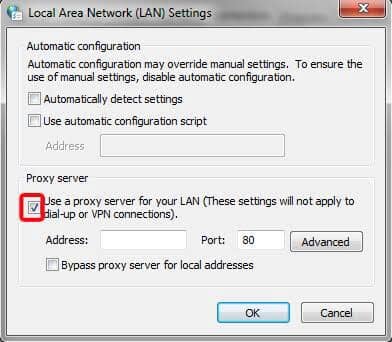
- Select your opinion, and Enter your IP Address and Port Number.
- For Local Testing to work correctly, you need to bypass the traffic for – bs-local.com – from your proxy. You can exercise this by clicking the "Avant-garde" push and calculation an entry in the 'Practice non use a proxy server for addresses get-go with:' text field.
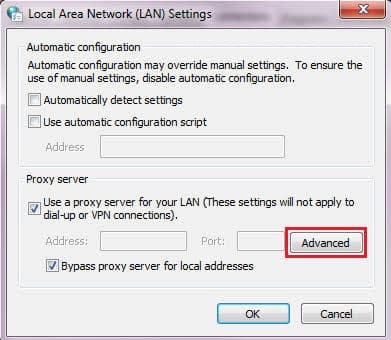
- Click on Ok.
Y'all may be similar to read,
- What is a Proxy Port? Default Proxy Port number 8080, 443, 3128
- 5 Ways to Find My Proxy Server Address (#5 is Awesome)
- Android Proxy 101: How to Configure a Proxy Server on Android
Firewall
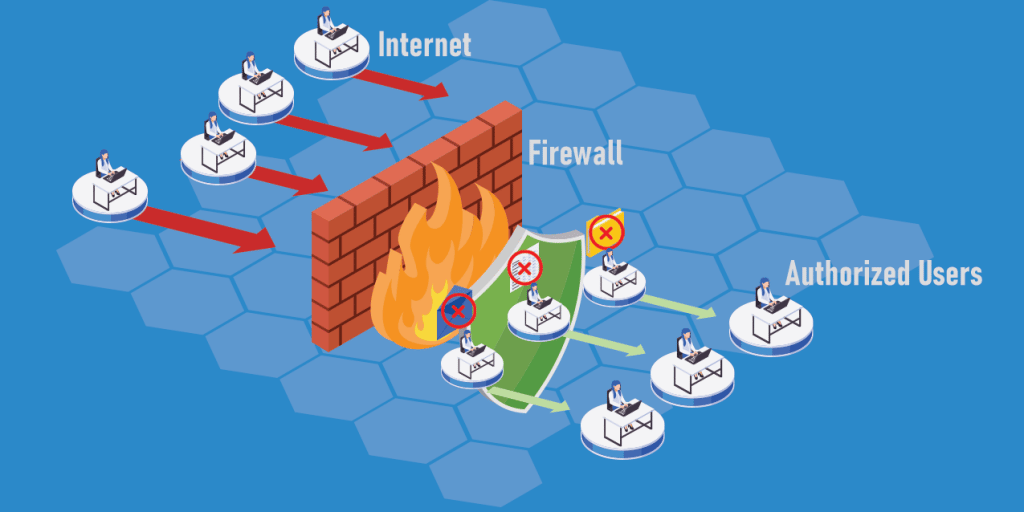
A firewall is a gateway that examines the traffic between the user and the computer. It is a consciously designed security organization that prevents unauthorized access from inbound a individual network by filtering the data that comes in from the internet. With the advancement of technology, firewalls are considered very essential in any organization, business, or even Personal Estimator (PC) in society to foster safety.
This blocks illegitimate traffic and gives admission to legitimate ones. In networking, this helps to end unpleasant situations from spreading wide and taking over an entire private setup past purposely standing as a bearer to the public internet.
The main target of this is to withhold hackers from maliciously penetrating networks and causing damage. Larger organizations purchase into the usage of firewalls in order to proceed their data privacy intact, hence no loss of information.
Certain rules are followed when using a firewall, and these rules can either allow or deny access. The rules are very sensitive and thus tin exist set in terms of IP addresses, ports, domain names, protocols, and keywords, among others.
Pros of Firewall :
- When having the idea of using a firewall, privacy is the commencement affair that comes to heed as information technology is actually an effect in the tech world today. Using a firewall equally a barrier to a security bridge tin can help foster a proficient network interface. This is because it has the capability to block unwanted traffic and allow wanted ones. Besides, it can block every activity rendered within its own network, therefore making it invisible to illegitimate malicious intruders trying to invade.
- The firewall has an admission control list that works with precise guarded rules to either allows or deny permission of the network. These rules are set past the network administrator to enable blockage of unauthorized traffics that can be unpleasant to the entire network setup. If an incoming or approachable request does not match the said rules, no access is granted.
- One major office of a firewall is to monitor incoming and outgoing traffic. Since information technology is customizable, network packet conveyance can hands be filtered based on several prepare rules. If whatever found threat is detected after a close watch, such network or data is blocked instantly.
- Unhealthy mischievous intrusion can completely render a network useless. This intrusion sometimes does come from within the setup system. But with a firewall, both the internal and external activities tin can be prevented from damaging and breaking down the unabridged network prior to when the illegal inversion is cleared.
Cons of Firewall :
- Even though some firewalls can be very expensive to set upwardly, an inexpensively cheap firewall can be less secured, and cause force inversion, hence, slowing down your network speeds.
- Firewalls are still very vulnerable to attack even though they have built lots of shields. The Software firmware, which seems to work at an operating organisation level, tin sometimes cause internal inversion, and so can the external ones.
- Some viruses tin can penetrate a firewall internally and sit on the network unknown to the firewall since, about times, they are designed to prevent threats trying to corrupt the setup from outside.
- A organisation that enables firewall security and suddenly disables it can be prone to harmful attacks since the reckoner is now openly accessing the public internet.
- Firewall upgrading in terms of maintenance is said to be very expensive and requires extra manpower considering it needs the expertise of an expert. Proper maintenance is required by experts; as such more than is ofttimes spent to continue it working.
How To Cheque Firewall Settings?
Switch Microsoft Firewall on, even if you already have another firewall on. It helps protect you from unpleasant access. To plough Microsoft Firewall on, beneath are the steps:
Step 1: Select the Start button
Step two: Click on Settings
Step iii: Click on Privacy & Security or Update & Security depending on your window version.
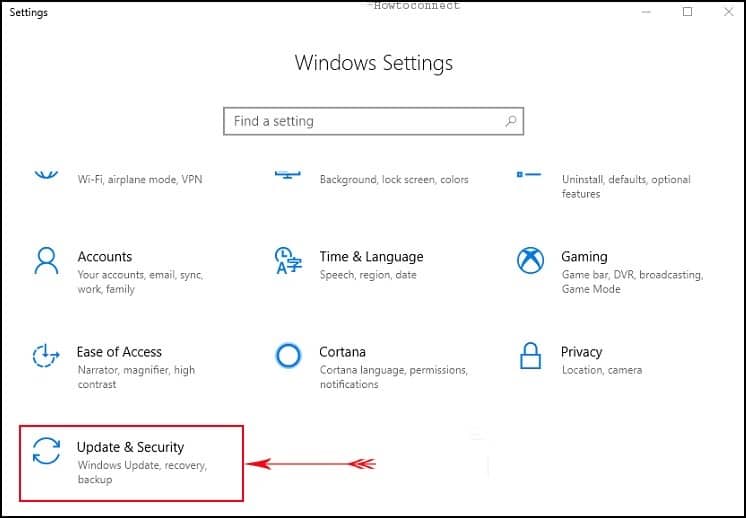
Pace 4: Select Windows Security
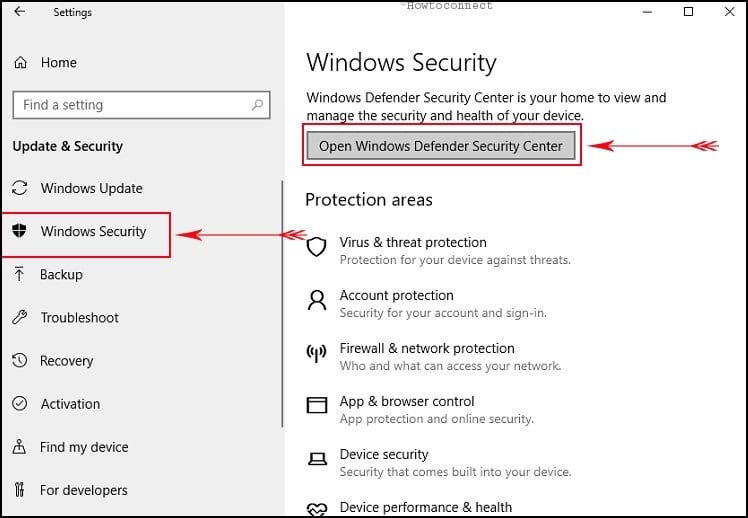
Pace v: Click on Firewall & network protection to Open Windows Security settings.
Step 6: Select a network profile either Damain network, Public network or Private network.
Footstep vii: Click Public network
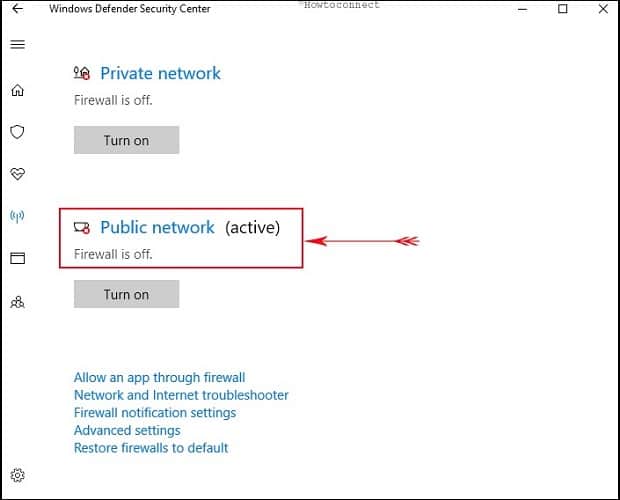
Step eight: Under Microsoft Defender Firewall, switch the setting to On.
Step 9: Click OK
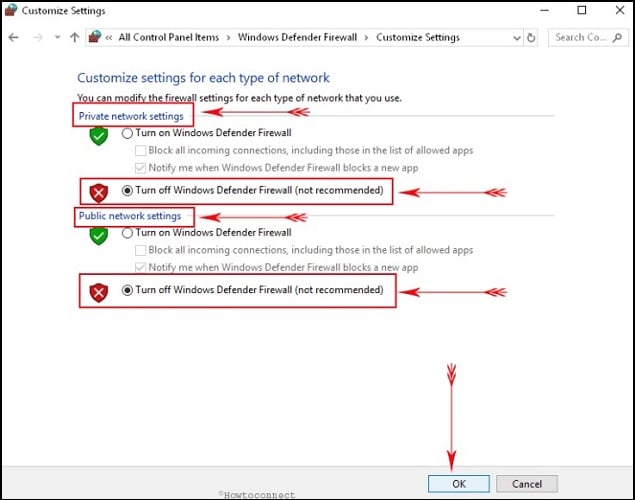
Stride 10: To turn information technology off, switch the setting to Off. Turning off Microsoft Denfender Firewall could brand your device (and network, if you have one) more than vulnerable to unauthorized access.
FAQs About Proxy and Firewall Settings
Q. Is Proxy the same as Firewall?
Proxy and firewall are both different parts of network security. Proxy stands as an intermediary to effectively mask your internal network from the public Net. Meanwhile, A Firewall is a gateway that prevents unwanted unauthorized access to your reckoner by blocking whatsoever malicious threat.
Q. Between Proxy and Firewall, Which is More than Secured?
Proxy and firewall are two networking security that operates differently with their own peculiar functionalities. The difference is that a firewall protects the internal network from unwanted threats and attacks. While the proxy server lets you utilize the Internet anonymously and featherbed restricted websites. However, both are widely used by various organizations and businesses; hence, they are important in their respective ways.
Q. What Does Domain, Private, and Public Network Mean in Setting a Firewall?
The Domain network controls traffic to a network, which uses the same domain controller as the server being administered. A private network controls traffic with the local server or network, which is by and large behind a NAT device, such as dwelling or small business networks. While the Public network controls traffic to and fro all networks other than domain networks.
Conclusion
Setting upward a proxy or firewall is an essential part of network security and also a secure way to get our computers guarded against malicious attackers, merely many don't seem to know this. In this writing, we have listed the steps on how yous can enable these system securities on your computers, be it personal or not, to keep your privacy unbridged.
Source: https://www.bestproxyreviews.com/how-to-check-proxy-and-firewall-settings/

0 Response to "How To Check Firewall Settings On Mobile"
Post a Comment